Topics
Introduction to Microprocessors and Organization of 8085
Instruction Set and Programming of 8085
- Introduction to Set and Programming of 8085
- Instruction Cycle
- Addressing Modes
- Programming model of 8085
- Introduction to Classification of 8085
- How to Write and Execute Simple Assembly Language Program ?
- Data Transfer Instruction
- Arithmetic Group Instructions
- Logical Group Instructions
- Branching Group Instructions
- Machine Control Instruction
Introdcution to Inted X-86 Family
Introduction to Microcontroller
Networking Technology
- Ethernet
- Token ring
Ethernet (Network Architectures)
Ethernet is a widely used local area network (LAN) architecture based on the CSMA/CD access method, also known as the IEEE 802.3 standard. It can utilize bus or star topologies, with "10" or "100" indicating transmission speeds in Mbps (e.g., 10 BASE 5 for 10 Mbps, 100 BASE-X for 100 Mbps). Ethernet uses baseband transmission, with wiring types designated by "T" for unshielded twisted-pair and "FL" for fiber optics. Data is transmitted in frames, ranging from 64 to 1518 bytes, with 18 bytes used for overhead.
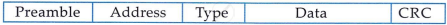
Ethernet Frame
A typical Ethernet II frame has the following sections :
- Preamble A field that signifies the beginning of the frame .
- Address A field that identifies the source and destination address for the frame
- Type: A field that designates the network layer protocol.
- Data: The data being transmitted.
- CRC: Cylindrical redundancy check for error checking.
10 BASE 2 (Ethernet topology)
The 10 BASE 2 Ethernet network uses thinnet cables, with each device connecting to the network via a T-connector attached to the network adapter. Key rules include a minimum 0.5-meter distance between clients, a maximum segment length of 185 meters, and a total network cabling limit of 925 meters. Up to 30 nodes (including clients and repeaters) can be on a segment, with terminators required at both ends. A network may have up to five segments, connected by no more than four repeaters, with only three segments hosting nodes, following the 5-4-3 rule.

10 BASE 5 (Ethernet topology)
The 10 BASE 5 Ethernet network uses an external transceiver to connect to the network adapter. Network segments are terminated at both ends, with one end grounded. Key rules include a minimum distance of 0.5 meters between transceivers, a maximum segment length of 500 meters, and a total network cabling limit of 2500 meters. Transceiver cables cannot exceed 50 meters, and each network segment can support up to 100 nodes.

10 BASE-T (Ethernet topology)
The 10 BASE-T Ethernet network uses UTP cables in a star topology, where nodes are connected to a central hub that acts as a multiport repeater. This setup is more reliable, easier to manage, and allows for simple troubleshooting, as faulty cable segments can be easily detected and repaired. A problem in one cable only affects the connected device, not the entire network. Key rules include supporting up to 1,024 computers, using UTP category 3, 4, or 5 cables (or STP), a maximum segment length of 100 meters, and a minimum cable distance of 0.5 meters between computers or hubs. 10 BASE-T is flexible and cost-effective for building LANs.

10 BASE – FL; 100 VG - Any LAN & 100 BASE – X (Ethernet Topology)
10 BASE-FL is an Ethernet specification for fiber-optic cables, supporting distances up to 2000 meters and avoiding electrical issues.
100 VG-Any LAN uses demand priority access with two priority levels, connecting computers to child hubs and then to parent hubs. It supports cable lengths up to 250 meters and transmits at 100 Mbps over twisted pairs.
100 BASE-X, or Fast Ethernet, uses a star-bus topology and also operates at 100 Mbps.
Token-Ring (Network Architectures)
Token ring uses a token - passing architecture. The topology is physically a star, but it uses a logical ring to pass the token from station to station. Each node in token ring is attached to a concentrator called a multistation access unit (MSAU or MAU). Because of MSAU, a single computer failure does not stop the whole network.
Token ring cabling
Traditionally, token ring uses twisted pair cables. The standard IBM cable types are:
Type 1: Uses two twisted pairs of solid copper wire with a braided shield for terminal and panel connections. Max distance: 101 meters (331 feet). Utilizes two STPs.
Type 2: Uses six twisted pairs (two STPs, four UTPs) for voice and data. Max distance: 100 meters.
Type 3: Uses UTP copper with two twists per inch. Lower cost but slower signal speed. Max distance: 45 meters.

Passing data on token rings
A token circulates around the token ring, and the computer holding it controls the transmission medium. The process is as follows:
- A computer captures the token.
- If it has data to send, it transmits a data frame while holding the token.
- Each computer checks if it is the intended recipient.
- The destination computer copies the frame, updates the status, and returns the frame to the ring.
- The sender receives the frame, acknowledges successful transmission, removes it from the ring, and releases the token back onto the ring.
Token ring frame

Start delimiter: Indicates the start of the frame.
Access control: Specifies frame priority and identifies if it's a token or data frame.
Frame control: Contains media access control info.
Destination address: Receiving computer's address.
Source address: Sending computer's address.
Data: The transmitted data.
Frame check sequence: Error-checking data (CRC).
End delimiter: Marks the frame's end.
Frame status: Confirms if the destination was found and the frame recognized.
