Topics
Exception Handling in Python
- Introduction of Exception Handling in Python
- Syntax Errors in Python
- Exceptions in Python
- Built-in Exceptions in Python
- Raising Exceptions in Python
- Handling Exceptions in Python
- Finally Clause in Python
File Handling in Python
- Introduction to File Handling in Python
- Types of Files in Python
- Opening and Closing a Text Files in Python
- Writing to a Text File in Python
- Reading from a Text File in Python
- Setting Offsets in a File in python
- Creating and Traversing a Text File in Python
- The Pickle Module in Python
Stack
- Concepts of Stacks in Python
- Operation on Stack in Python
- Implementation of Stack in Python
- Notations for Arithmetic Expressions in Python
- Conversion from Infix to Postfix Notation in Python
- Evaluation of Postfix Expression in Python
Queue
- Concept of Queue in Python
- Operations on Queue in Python
- Implementation of Queue using Python
- Concept of Deque in Python
- Implementation of Deque using Python
Sorting
- Introduction to Sorting in Python
- Bubble Sort in Python
- Selection Sort in Python
- Insertion Sort in Python
- Time Complexity of Algorithms in Python
Searching
- Introduction to Searching in Python
- Linear Search in Python
- Binary Search in Python
- Search by Hashing in Python
- Collision Techniques in Python
Understanding Data
- Concept of Data
- Data Collection
- Data Storage
- Data Processing
- Statistical Techniques for Data Processing
Database Concepts
- Introduction to Database Concepts
- File System
- Database Management System (DBMS)
- Relational Data model
- Keys in a Relational Database
Structured Query Language (SQL)
- Concepts of Structured Query Language (SQL)
- Data Types and Constraints in MySQL
- SQL for Data Definition
- SQL for Data Manipulation
- SQL for Data Query
- Data Updation and Deletion
- Functions in SQL
- GROUP BY Clause in SQL
- Operations on Relations
- Using Two Relations in a Query
Computer Networks
- Concept of Computer Network
- Evolution of Networking
- Types of Networks
- Network Devices
- Networking Topologies
- Identifying Nodes in a Networking Communication
- Internet, Web and the Internet of Things
- Domain Name System (DNS)
Data Communication
- Introduction to Data Communication
- Components of Data Communication
- Measuring Capacity of Communication Media
- Types of Data Communication
- Switching Techniques
- Transmission Media
- Wired/Bounded Transmission Media
- Wireless/Unbounded Transmission Media
- Mobile Telecommunication Technologies
- Introduction to Protocols
- Types of Protocol
Security Aspects
- Threats and Prevention
- Malware
- Antivirus
- Spam
- HTTP vs HTTPS
- Firewall
- Cookies
- Hackers and Crackers
- Network Security Threats
Project Based Learning
- Introduction of Project Based Learning
- Approaches for Solving Problems
- Teamwork
- Project Descriptions
CBSE: Class 9
Spam Emails and Their Risks
1) Purpose and Caution in Using Email
- Email is widely used to send and receive messages, documents, and information across the Internet.
- However, users must be cautious, as not all emails are safe.
- Some emails may come from unknown or suspicious sources and try to mislead or trick users these types of emails are called spam emails.
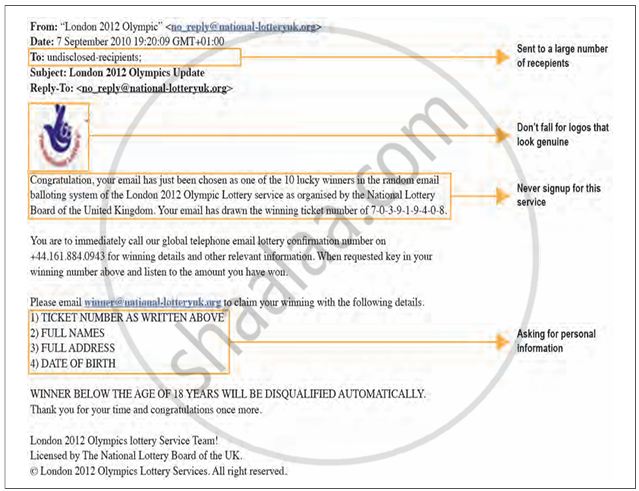
2) Examples of Suspicious Emails
-
Example 1: An email claims to offer a popular game worth ₹3,500 for free and asks you to download it. Risk: The file may contain malware (malicious software) that can harm your device.
-
Example 2: An email contains a link asking you to verify your account details. Risk: Clicking the link might redirect you to a phishing website that steals your personal data.
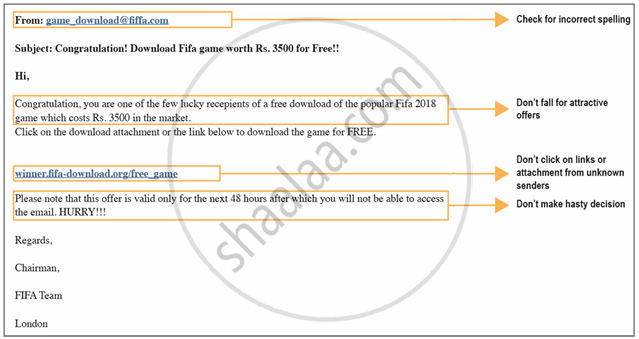
3) Identifying Common Signs of Spam Emails
- The email is from an unknown sender.
- The subject line sounds too good to be true (free gifts, prizes).
- Contains urgent requests for personal details.
- Encourages you to click unknown links or download attachments.
- Poor grammar, spelling mistakes, or a suspicious-looking sender address.

